CIS Benchmarks for AWS with CloudHealth and VMware Secure State
One of the core foundations for IT organizations is Security. Everyday we hear of new stories and the repercussions of every breach; from Personal Information to Intellectual Property, security is paramount to business and organizational success.
Over the past few years, IT organizations have spent countless resources to ensure their applications and infrastructure are meeting the daily challenge to remain secure. The proliferation of Public Clouds is something I hear when speaking with Security team. Two years ago, a CISO told me that he had to prevent an application team from rolling a new solution to production because he was struggling to secure their AWS workloads. To be fair, AWS is not insecure by default. Humans are the reason an S3 bucket is open to the world or that AWS Shared Keys end up on a GitHub repository. I should write about the few times this has happened to my team, one of them was my fault.
My goal with this blog is to introduce the reader to VMware solutions for meeting everyday security needs with a focus on CIS® Benchmarks with CloudHealth and VMware Secure State.
What is CIS® anyway?
I was first exposed to CIS (Center for Internet Security) at the onset of my IT career way back in the early 2000s. At that time, I was responsible for the Operating Systems securing several thousand physical servers and countless desktops and laptops. In the end, I utilized CIS; among others; to ensure the security posture for the Operating Systems and infrastructure related solutions. You can check out the CIS website for yourself but for reference I picked a few highlights from the About Us page.
CIS Vision
Leading the global community to secure our connected world
CIS Mission
- Identify, develop, validate, promote, and sustain best practice solutions for cyber defense
- Build and lead communities to enable an environment of trust in cyberspace
Benchmarks for Weekend Reading
There are many resources available to IT practitioners as it relates to CIS Benchmarks for the various public clouds. CIS provides a web site to access the extensive list of Benchmarks available. There are benchmarks available for Operating Systems, Network Devices, Cloud Providers, etc. I am still a bit disappointed that CIS Benchmarks™ are no longer updated for Multi Function Print Devices.
CIS Benchmarks™ are a set of configuration guidelines to safeguard systems against todays cyber threats.
In addition to CIS itself, each public cloud vendor provides their own respective guideline to meet CIS Benchmarks™. Below are a few links to the respective guides from AWS and Azure. Each of these are guidelines for building a reference architecture for applications and the cloud infrastructure in which they reside.
Amazon Web Services: CIS Benchmark on AWS
Microsoft Azure: CIS Microsoft Azure Foundations Security Benchmark
While each of these are fantastic resources, the practicality of each seems to get in the way. Navigating the reference architecture, specific controls and items can be a daunting task. Take it from me, weekend reading of Security, Compliance and Governance guidelines is inevitable for a DevSecOps professional but I would never call it exciting.
Benchmarks for the Real World
I will be the first to admit that tooling is a bit overwhelming and there are hundreds if not thousands of solutions available to meet the needs of IT organizations. Some of these solutions have been on the market for decades and continue to provide support day in and day out.
Over the next series of blogs, I am going to highlight several VMware solutions that are available to organizations to meet the needs of CIS Benchmarks™ for AWS.
CloudHealth by VMware
One of the out of the box dashboards from CloudHealth is Health Check.
The next screen allows us to choose the security policy used for this view
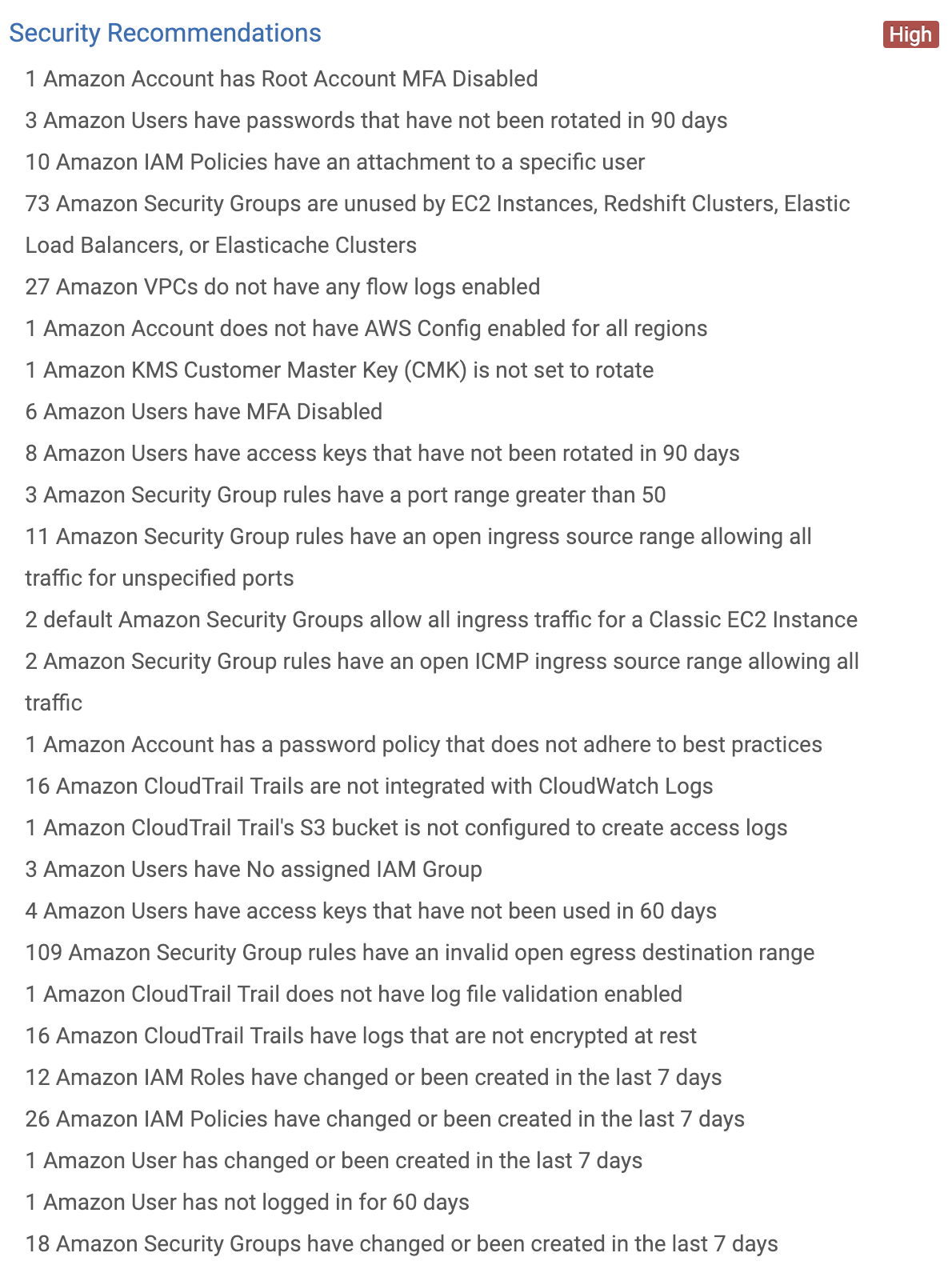
After selecting CIS AWS Foundations and updating the view we are presented with several optimization recommendations. Not only do you have a quick overview of things like Monthly Savings from a Cost point of view, Cloud Governance for proper ownership but we also have the overall security posture as it relates to the CIS Foundations for AWS.
Security Risk Exposure is a high level overview of my organizations AWS environment in relation to the CIS Benchmarks™ or configuration guidelines.
I will be the first to admit that this environment needs some cleaning up but it also provides within a few clicks the overall posture for my AWS accounts. Not only will CloudHealth provide the reporting mechanism within the UI, but actions can be taken such as an email send per violation.
VMware VMware Secure State
VMware also has a new solution based upon an acquisition of a Seattle based startup called CloudCoreo. VMware Secure State is a SaaS based solution to help your organization meet the demands of security audits. While it may seem similar to CloudHealth in overall content; CIS Benchmarks™, VMware Secure State number one focus is security audit and governance. One of my favorite aspects of VMware Secure State is the goal of bring Security and Controls validation into the CI/CD pipeline, more on that in a later blog!
Below is an overview screen from the VMware Secure State dashboard. VMware Secure State is purpose build to bring multiple public clouds; and each independent account, into a single view for Multi-Cloud consumption.
Once again, this environment needs some work, I get it!
One of the ways VMware Secure State lends to Real World application is in the ways the data is presented and represented.
Compliance
Compliance is one of the outcomes of a secured IT application and related infrastructure. The definition of **Compliance **varies by organization and vendor solution. For VMware Secure State, the goal is to ensure compliance of Benchmarks, Frameworks, etc.
Notice the breakdown of CIS AWS Foundations and NIST standards. While I am focusing on CIS in this blog, VMware Secure State expands beyond CIS® and into NIST Frameworks.
This organization is not 100% compliant as it relates to CIS™ and NIST.
Violations
To help further break down the recommended controls, VMware Secure State highlights violations or controls that are currently not meeting expectation.
As you can tell VMware Secure State provides deep insight into EC2, RDS, S3 VPCs and so on. In this view, not only are we looking at CIS but also NIST in relation to my selected environments.
Below are a few examples of day to day issues that we have seen from many customers and the ease of use in which to highlight and identify the shortcomings.
RDS Snapshots not encrypted
List views of all snapshots that do not meet the standards.
Below is an individual view for one of the respective RDS resources that is not up to security standards.
While there are many ways to remediate violations, VMware Secure State wants to begin the journey through proper notification and clarification. Remediation is in the works, more on that in a later blog.
Available Actions
- Suppress —Suppress a violation for a specific object or even the rule across all assets.
- File Ticket — Create a JIRA ticket
- Share — Slack support, no more email!
Practical Compliance, Security and Governance
While the VMware journey for Multi-Cloud is only beginning, Security has been and is apart of our DNA. As a software company, we have spent countless hours ensuring our solutions meet security demands from the smallest of organizations to the largest of customers in the world.
Start utilizing CloudHealth by VMware and VMware VMware Secure State today to provide a practical view of your Security, Compliance and related Controls in a Multi-Cloud World.
Stay tuned for a follow up to this blog where I dig a bit deeper into the details and even highlight some additional actions that can be taken utilizing CloudHealth Actions.






